Healthcare still needs to learn how to protect patient data.
 |
| By: Brand Barney |
One of the best things a business can do to protect credit card data is
segmentation, or, reducing the places that can touch card data during and after card processing. The fewer places card data touches, the fewer places protection is needed.
But that doesn’t work for healthcare. You can’t segment Protected Health Information (PHI) within a healthcare environment. In truth, it needs to be everywhere to enhance patient healthcare.
The real security hiccup in healthcare HIPAA security is, healthcare organizations don’t think about all the places PHI is. Because they don’t think about where the data is, they don’t know what vulnerabilities put that data at risk. And because they don’t know the vulnerabilities that put their PHI at risk, they can’t and don’t protect their PHI.
You’ve got to take a giant step back and think, “Where is all our patient data?” Let me give you a hint. It’s not all in your EHR.
Which organizations have PHI?
Think of organizations that likely have access to your health information. Three entities probably come to mind: a doctor’s office, hospital, and health plan.
But there are so many more entities that fall under the gargantuan umbrella of those who access PHI. And if they have access to PHI, that means they must also
comply with HIPAA. Let me give you just one true
example of an entity who has no idea they’re a covered entity under HIPAA regulations.
PHI at summer camp
A troubled child who needs special attention gets sent to a summer camp to receive social therapy. As part of the summer camp, the youth counselor must provide feedback to parents. So, he takes pictures (via his smartphone) of kids having fun and uploads the photos, along with his medical notes and the child’s name, on an unsecured portal that doesn’t require a login to access.
The therapist regularly meets with the child to discuss how he’s doing. He takes rigorous notes on a notepad about drug abuse history, what medications the child is taking, how he’s feeling, who he gets along with, etc. The therapist keeps the notepad in his truck, and at the end of the day he enters the data into his EHR at home. He keeps the physical notepads in his basement/attic when he’s finished.
Whoa, what just happened in this example?
- This organization definitely collects PHI about the child
- They take pictures on an unsecured smartphone
- They upload the child’s name, medical data, and pictures (all PHI) onto an unsecured site
- They allow PHI to be stored inside an employee’s unlocked truck
- They allow PHI to be stored in an employee’s basement/attic! (Is that paper PHI secure, and how long is going to be stored?)
This may seem like an extreme example of total insecurity, but it’s not. I see situations like this almost every time I
audit healthcare organizations.
Where is PHI within an organization?
So now that we know many organizations store PHI, how are they storing it at their organization? Let me give you a few true scenarios.
Paper
Receptionists and nurses don’t interrupt the doctor with messages from patients who call in. They take messages on notepads, sticky notes, and copy paper. Typically, that info (including PHI) is given to the doctor later. Usually, the doctor takes his notes in his office, follows up with them, but
DOES NOT secure the data.
In the doctor’s office desk drawer, chock full to the brim, are those notes containing PHI. Patient notes, phone numbers, questions about pills, etc. The desk isn’t even secured with a key (there usually is a key, but it’s not in use.) I estimate most doctors’ offices have a drawer/closet/area full of mail and PHI ranging back a few years.
Why does this happen? To put it as gently as possible, the provider is usually too busy or too lazy (doesn’t see the security risk, threats and vulnerabilities to PHI) to walk around the corner to the cross-cut shredder, or follow office/company policy.
Test environments
When entities develop a product, many use test environments to check the product is performing correctly. For some reason, healthcare always uses live production data in their test environments. Why they would use real patient data is beyond me. If an individual can access the test environment, that means they could also steal the live data off that environment. My recommendation is to use test data only.
On computers
Patients get left inside exams room to take surveys on open computers all the time. Many of those computers also have access to the EHR. If they merely minimized the survey and opened the EHR, or access your shared network drive that isn’t protected, they could plug in a USB and copy the data without anyone knowing. Especially if you don’t have the proper systems in place to alert you that any of this took place.
Check out the infographic below for a
list of places most healthcare organizations store PHI.
If I was a hacker… (example)
If I was a hacker, here’s how I would steal your PHI.
I would get hired on as part of your janitorial staff. They have keys to everything, and it’s not hard to get a job as a janitor (no offense to janitors). You would never know I stole your data, because I would just take pictures of it with my phone. Most healthcare entities don’t do background checks on their janitorial staff, so even if I had a previous record, I could probably still get a job.
If I didn’t want to start as a janitor, I could start as another member of your organization … even with a criminal background.
Most organizations don’t run background checks on employees hired internally. If I wanted to, I could start in the marketing department (typically no background check) and eventually move to a different department (like IT). As a system administrator, I would have total database access. All I would have to do is select everything inside the database and download it to a café network so the feds can’t trace it back to me.
Piece of cake. (Well maybe not quite a piece of cake, but you get the idea)
SEE ALSO: HIPAA Security vs. EHR Security
Hacker’s don’t just care about your EHR
It’s important to understand how a hacker thinks. Hackers want all of your data, all of your PHI, all of the time. If they can get into your EHR, they will and they will take that data too. However, there are a million other easier ways to get that data that doesn’t involve cracking into your EHR.
Besides an EHR, here are easier places hackers can access if they want to steal PHI:
It’s on exam room computers
Many healthcare entities enter PHI data on workstation computers (in exam rooms, in the pharmacy, etc.), and then copy that information to their EHR. Usually, these computers only have one username and one password. Usually the username is easily guessable, such as Exam1.

If a hacker can access that exam room computer by cracking an easily guessable password, he doesn’t need the EHR. The data is all right on that computer. But if he really wants to get into the EHR, all he needs to do is download keylogger malware that records the EHR password as it’s being typed.
It’s on passwordless network shares
When data is entered on workstation computers, it’s typically also uploaded to some sort of network share accessible to the entire healthcare network. That way, billing and other departments can pull the data off the network share instead of access the data via the EHR. While this is extremely convenient for healthcare, it also makes a hacker’s job easier.
Typically, everyone in that healthcare environment has access to the network share, because the organization doesn’t use
role-based access control. In addition, practically no healthcare network shares have passwords.
It’s unencrypted and in your Downloads folder
What happens when you download something from a network share? Well, it goes straight into whatever folder your computer has configured for downloads, which is usually some sort of Downloads or My Documents folder. Remember, this sensitive patient data is UNENCRYPTED.
Now… how long does the data remain in that folder? And how long does it remain in your trash folder after you delete it? And
when you finally delete stuff out of your trash or recycle bin, do you use a secure delete method?
It’s on your home network
If the doctor uses
unprotected remote access to access patient files from home, he probably pulls the data from the healthcare network. He may also be using email for business purposes on his home computer and saving files locally with PHI in them. If the hacker can simply break into the doctor’s home Wi-Fi, he now has even easier access to the PHI.
Why is unprotected PHI so dangerous?
Patient health information, like Social Security Numbers, are not like credit card information. The credit card brands know every card that’s assigned to every individual. When a business begins to lose data from a credit card breach, the card brand can quickly flag that trend and report a data breach.
Flagging potential medical identify theft just doesn’t happen in healthcare. And maybe that’s a good thing. Americans don’t necessarily want Big Brother looking over their shoulder and knowing all their medical data. But how else can we track medical fraud?
Here’s another scary thought.
Credit cards are disposable. If your card is compromised, you immediately have it canceled and they send one with new numbers in two to three days. Healthcare data is not disposable. You can’t just send your Social Security Number in to have it replaced every year. Because healthcare data is valuable for the foreseeable future, a hacker could steal your PHI and sit on it for 20 years without it degrading in value.
Because of its value, medical fraud is a lot less forgiving than credit card fraud.
Fixing the unprotected PHI problem
No Big Brother is looking out for healthcare entities, so you’ve got to look out for the security at your own organization. The unprotected PHI problem is easy to fix, but it must start with you. Remember these tips.
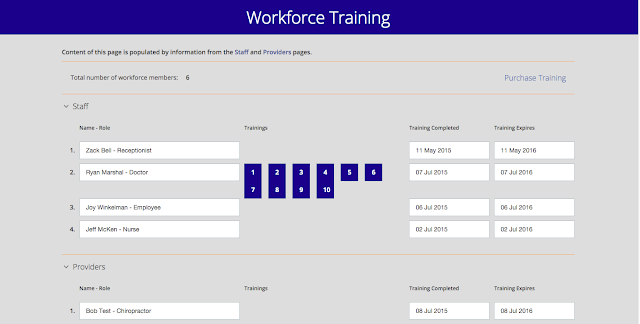
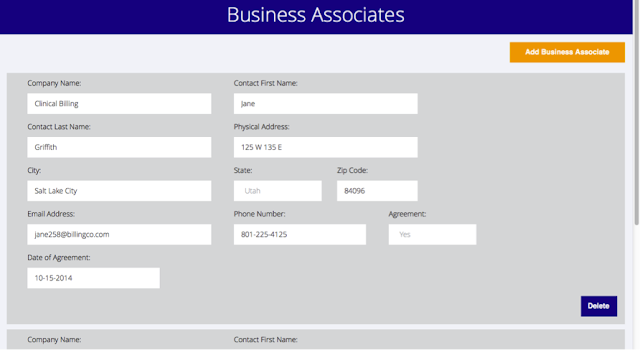
Get a free HIPAA compliance dashboard demo.
- Be noisy when you see problems in your organization. You are responsible for the data that you interact with, collect, transmit, maintain, and by golly you’d better protect that data. If your CFO effectively says, “We don’t protect PHI because we don’t have the budget,” harp him until you get the budget.
- Don’t let your doctor (or hospital admin, or IT director) hold you back on security. If you see your doctor shoving yet another patient note in his unlocked drawer, tell him no!
- Sit down in a meeting with your staff and admit your organization has problems. Ask your staff to identify those problems, because I guarantee they’ve seen them.
- Engage a security professional to identify your risks for you. Be active in the health of your security because that’s an active role.
Group mentality is slowly killing healthcare’s PHI security. Don’t be the fish that thinks the shark can’t get him because he’s one of a million other fish. What he doesn’t realize is, the fish right next to him is stealing all his data right under his cute little flipper.
Don’t forget to check out the infographic below for a condensed list of places most healthcare organizations store PHI.
Brand Barney (CISSP, HCISPP, QSA) is a Security Analyst at SecurityMetrics, has over 10 years of data security experience, and will totally geek out if you mention Doctor Who. Brand loves to play jazz piano and daydreams about being as great as Dave Brubeck or Thelonious Monk. Connect with him on Twitter or check out his other blog posts.



 I’ve seen some pretty wild HIPAA violations from the viewpoint of both auditor and patient. The
most common violations I see at reception desks are things like:
I’ve seen some pretty wild HIPAA violations from the viewpoint of both auditor and patient. The
most common violations I see at reception desks are things like:














![PHI: It’s Literally Everywhere [Infographic]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgYwwYkbPWFj9D79IRJI231W9orz0Aoq7TpPD0ptPa1Mabq51fYYTjKtSYIvxlweCCHNg22w5DeoPFA5ZMJ3G0YZQ_BYufRgy-4rW6Gy47pvETk67L2o6edvGmLrnMWyPtSX7-denKFNjY/s72-c/Unsecured+PHI_Blog.png)