Payroll Phishing Emails Attack Hospital and Healthcare Security
Hackers aren’t always after patient records.
 |
| By: Aaron Willis |
But… there are other options for hackers looking to make a quick buck (or lots of bucks) while attacking healthcare, such as exchanging trade secrets…or stealing paychecks.
In fact, I’ve personally seen an increase in successful phishing attacks targeting information other than medical data in a hospital environment. According to Sophos, 156 million phishing emails are sent every day, and 80,000 people fall for them. Every day.
Payroll phishing: How it works
 Using somewhat mundane phishing attack methods, attackers can hijack a hospital’s employee payroll and reroute the money to anonymous bank accounts.
Using somewhat mundane phishing attack methods, attackers can hijack a hospital’s employee payroll and reroute the money to anonymous bank accounts.Here’s how it’s done:
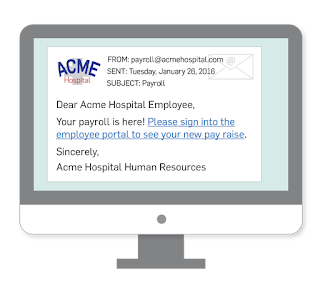
- An attacker designs a phishing email to look like it came from the hospital’s Human Resource (HR) department.
- The phishing email is sent to targeted, or all, hospital employees.
- The employee clicks on a link in the email that takes them to a fake employee portal login page.
- After the employee submits their information for login, the attacker captures the credentials.
- Using the stolen credentials, the attacker logs in to the employee payment network and changes the routing and account numbers on the employee’s direct deposit page and waits for the next pay cycle.
How could payroll phishing happen?
I know what you’re thinking. “You'd have to be pretty stupid to fall for that!” Well I can tell you more than one neurosurgeon has, and they are pretty smart cookies.But how would an attacker make it look like an email came from an internal HR department? There are protections in place right?
Well hopefully, but let’s go through the above steps again and add just a little more sophistication as I walk you through this example phishing hack.
1. An attacker designs a phishing email to look like it came from the hospital’s Human Resource department.
All too often hospitals are prime targets of social engineering attacks that can expose what seems like benign data. A single email from HR will often have everything needed, including actual staff names, to craft a believable email. If that doesn't work, borrowing logos and other resources from the hospital website can get the job done.
2. The phishing email is sent to targeted, or all, hospital employees.
This is the most difficult part of the attack. An attacker needs email addresses and most websites don’t have many emails listed. But attackers notice email naming conventions, such as: first.last@victimhospital.org. Some hospitals have a list of their top doctors, so if an attacker puts two and two together...
An attacker’s first attempt to send an email with a spoofed from: sam.secretary@victimhospital.org will probably fail because...IT checks for attacks like that. But clever hackers will likely send the email again from sam.secretary@victimhospital.net. The email will probably go through. Of course 20 minutes prior, they registered victimhospital.net with a stolen credit card.
3. The employee clicks on a link in the email that takes them to a fake employee portal login page.
Renowned neurosurgeon Dr. Ima BrainStein gets an email from Sam in HR saying “Hi Dr. Brainstein. You received a raise. Please login to the employee portal to confirm.” Dr. Ima clicks on the employee_portal.victimhospital.org link which redirects to the spoofed employee_portal.victimhospital.net page which is remarkably similar to the real login page.
4. After the employee submits their information for login, the attacker captures the credentials.
After logging in, Dr. Ima Brainstein is disappointed by the message. “Sorry, the employee portal is down for maintenance. Please try again in a few minutes.”
The attacker is not not disappointed, as he just captured Dr. Ima’s credentials:
username: “brainstein.ima”
password: “I_got_my_D3gree_online!”
5. Using the stolen credentials, the attacker logs in to the employee payment network and changes the routing and account numbers on the employee’s direct deposit page and simply waits for the next pay cycle.
Phishing attacks are a very serious crime and happen more frequently because they are relatively easy to pull off.None of the steps above took stellar hacking skills, just a basic understanding of how email and domain names work.
See Also: Fighting Phishing Email Scams: What You Should Know
Hospital vulnerabilities
Of course there are much more complicated attacks that involve exploiting obscure vulnerabilities in web servers, email servers, and various web protocols. But unfortunately many hospitals are riddled with simple vulnerabilities.A vulnerability is a flaw in components, procedures, design, implementation, or internal controls. Countless vulnerabilities exist in the healthcare industry today, such as weak passwords, unpatched software, negligent employees, coding problems, and misconfigured firewalls. Not to mention massive amounts of sensitive data walking in and out the front door into the wild west of employee's home computers, personal laptops, and mobile devices.
Here are a few of the most likely vulnerabilities that could allow a payroll phishing or other attack to occur.
Employee training (or lack thereof)
 Healthcare employees are the largest unavoidable threat to healthcare data security. Many can be socially engineered, use weak passwords, and surf the web unrestricted at work. They walk out the door every day with a million bucks worth of HIPAA fines on a personal laptop protected with the password: password.
Healthcare employees are the largest unavoidable threat to healthcare data security. Many can be socially engineered, use weak passwords, and surf the web unrestricted at work. They walk out the door every day with a million bucks worth of HIPAA fines on a personal laptop protected with the password: password.Work from home wonders
Healthcare IT staff goes to great lengths to make remote access a smooth experience for the many telecommuters that work in the industry. They set up bulletproof VPN's and two factor authentication and create the perfect firewall rule set. Then while using public Wi-Fi on a beach in Maui, a hacker breaks into the laptop. The hacker is now a user on the internal network.
Physical security…or the lack thereof
Healthcare environments, especially hospitals, have a difficult time controlling their location’s physical security, and the physical security of protected health information (PHI).
Here are some examples of physical security problems I see when I walk into hospitals:
- Wi-Fi security: It is not uncommon for random people to walk into hospital lobbies and mooch some free wireless Internet. Most of the time this is benign, but what if that person is an attacker? How secure is the customer/patient Wi-Fi? What if employee laptops and devices are connected to the public Wi-Fi instead of the protected internal Wi-Fi?
- Empty nurse stations: What happens when the shifts change and the nurse station is abandoned for hours on end until the next shift? Nobody is monitoring it. An outside person could plug right in to the network through that nurse station or simply plug in a hidden USB wireless access point and leave.
- Employee mobile device hotspots, Bluetooth connections: Out of habit when doing onsite security assessments, I scan for wireless signals and devices. I am rarely disappointed. What good is a locked door or fingerprint scanner if a hacker can compromise a wireless device on the other side?
Difficult third party vendors doing their own thing
Most hospitals have a great internal IT staff who know what they are doing, security-wise. But, they’re overwhelmed due to inherent maintenance/control/enforcement nightmares inside hospital politics. A top producing business associate, such as a pharmacy, may have its own ideas and different rules for its own network. To keep high-producers happy, security policies have a habit of developing short-sighted, though financially expedient, exceptions. The cycle is not favorable for hospital and healthcare security.
Avoiding attacks
The good thing is, all of these vulnerabilities can be managed. Here are some great ways to avoid attacks like the payroll phishing attack at your healthcare practice.- Security policy: Create a comprehensive security policy that addresses every bit of data that comes in and goes out of hospital. Invite all stakeholders to participate in developing a comprehensive policy. Most stakeholders will be easy to work with when they understand the risks and vulnerabilities that must be managed. (Download a free HIPAA security policy here.)
- Secure the email server: Be aware of all email methods such as software and web services that have the ability to send email, and be certain their activity is validated against email policies.
- Business associates: IT staff must have the support of upper management when enforcing unpopular IT policies. Management should understand the risks and the possible and probable costs of an eventual data breach when they agree to let the gift shop run their own payment network, or the restaurant have its own customer Wi-Fi.
- Control the SneakerNet: Are you controlling the data walking in and out the front door every day? Security policies should cover personal computer/device usage including thumb drives and mobile phones. What is the protocol if an employee loses a laptop, tablet, or device that contains sensitive information?
- Employee training: While employees remain an ongoing risk, ironically they are also one of the most reliable and best ways to protect healthcare data. A properly trained employee can spot problems before they become problems. Your workforce has a thousand eyes and ears that can be trained to catch what your overwhelmed IT staff misses. Every employee should be trained to spot things like phishing attacks and detect common social engineering tactics. Employees should attend security policy training at least once a year and know how it pertains to their job both at work and home. While employee training will not prevent every breach, it can certainly reduce the count.
Hospitals: prepare for more attacks
Payroll phishing is a relatively easy way for hackers to rake in the dough. It does take some luck, but I predict we will see more attacks like this as more attackers realize the inherent value not just in healthcare data, but exploiting the employee data of all those who work in the healthcare industry. When strategizing and planning for HIPAA compliance, remember that enforcing the policies procedures surrounding hospital and healthcare security are crucial to protecting patient and employee data.Prior to becoming a Forensic Analyst for SecurityMetrics, Aaron Willis had over 15 years of diverse experience in all aspects of IT security, business intelligence, data mining, SaaS consulting, and programming. In addition to being the VP of Technology and Information Systems at ScrapeGoat, Inc, Willis teaches Information Systems as a professor at Utah Valley University. Willis holds a Bachelor’s in Computer Science from Utah Valley University and is currently working on a Masters in Digital Forensics. His certifications include: CISSP (Certified Information Systems Security Professional), QSA (Qualified Security Assessor) and PFI (PCI Forensic Investigator).

